Can you track a stolen laptop without GPS?
Yes — to an extent. Without GPS, a stolen laptop is usually tracked using the last-known active location at city or region level, plus device activity signals such as timestamps, account access history, and audit logs. This will not show an exact street address, but it can provide useful evidence for internal investigations, insurance documentation, and security workflows.
- Best for: last-known city or region, time of last activity, and location history patterns
- Not for: live GPS pin-point tracking or exact street location
- Reality check: if the device never comes online again, you can only use the last recorded location
What to do in the first 24 hours
When a laptop is stolen or lost, speed matters. Here is a practical first-day workflow many IT and operations teams follow. Adjust it to your own policies and local rules.
- Confirm the device: device name, serial or asset tag, assigned employee, and last known user.
- Check last activity: when was the laptop last active, and from which city?
- Secure accounts: reset passwords, revoke sessions, rotate tokens, and protect critical apps.
- Start the incident process: open a ticket, assign an owner, and document each action.
- Export evidence: last-known location, timestamps, and location history for internal reporting or insurance workflows.
What you can and cannot learn without GPS
Many people expect live GPS tracking. In reality, most business-friendly tools focus on last-known active location and device activity logs.
What you can learn
- Last known city where the laptop was active
- Time and date of last connection
- Location changes over time through location history
- Unusual patterns, such as sudden country or city changes
What you usually cannot learn
- Live GPS position of the device
- Exact street address
- Accurate location while fully offline
- True city if a VPN is constantly used
This is one reason privacy-first tracking is often preferred in workplaces: it supports security and audit workflows without turning into invasive real-time surveillance.
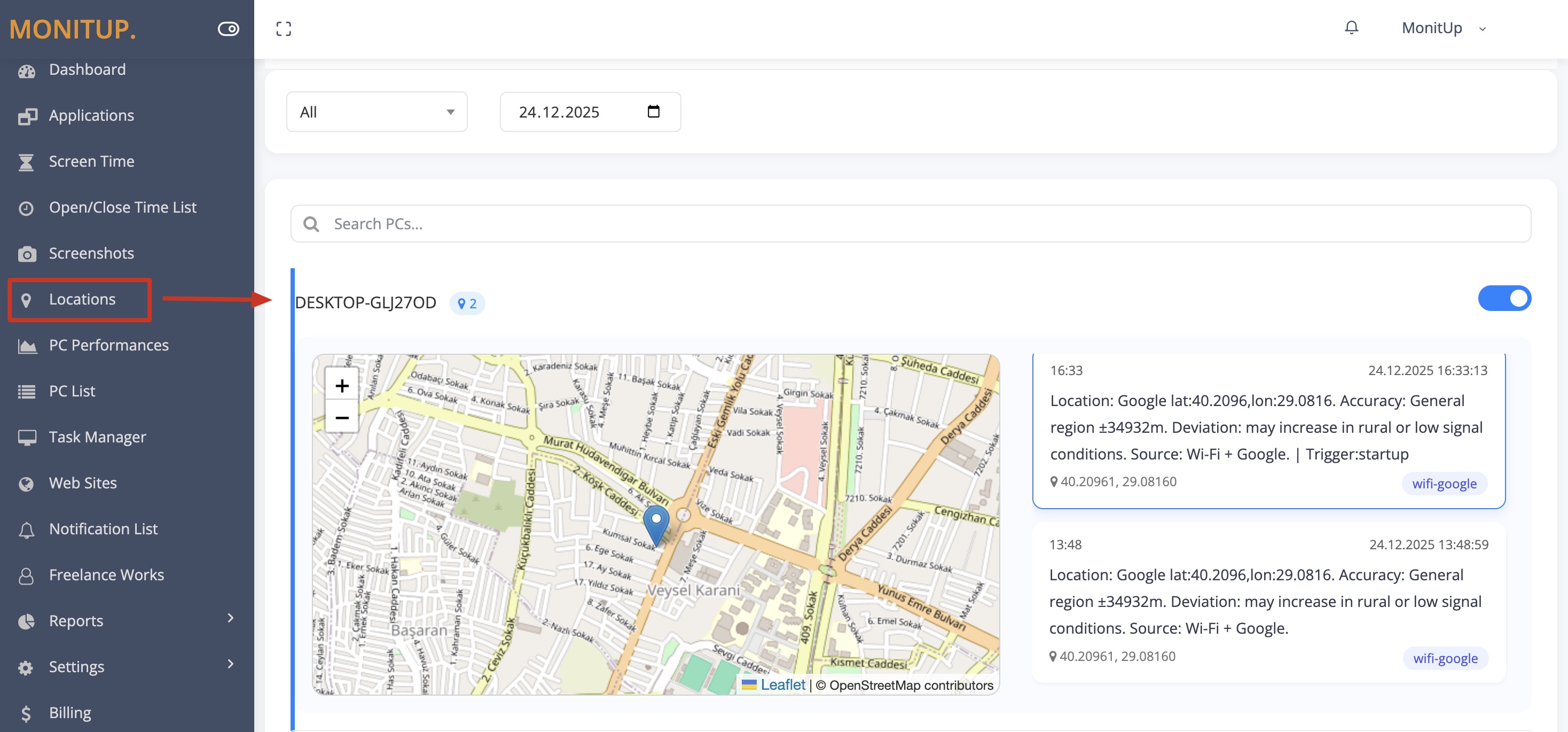
How MonitUp helps track stolen laptops
MonitUp’s approach is built around something practical and auditable: record the last-known device location at city level when a Windows laptop is active, and keep a clear history that admins can review and export.
1) Capture
The Windows device reports activity signals while it is in use, creating the basis for last-known location records.
2) Resolve
Network-based signals are resolved into a city-level location rather than exact live GPS coordinates.
3) Store
Each record includes timestamps and builds a location history timeline for later review.
4) Report
Admins can review the last-known city, timeline changes, and export records for incident reports or audits.
What evidence to export
If your goal is to support an internal investigation, insurance claim, or security review, export a clean set of records. This is where stolen laptop tracking becomes genuinely useful.
- Device identity: device name or ID, assigned user, asset tag
- Last-known location: city plus timestamp of last activity
- Location history: the recent timeline, if available
- Audit logs: who accessed records and when
- Security actions: account lock, session revoke, or password reset times
VPNs, accuracy, and common limitations
City-level tracking is practical, but it has limits. Understanding them reduces false assumptions during an incident.
- VPN impact: the visible location may be the VPN exit city, not the laptop’s actual city.
- City-level precision: useful for region or city, not street-level pinning.
- Coworking spaces and hotspots: shared networks can reduce precision.
- Offline devices: no new records appear until the laptop is active again.
If the laptop never reconnects
Sometimes the device never comes online again. Even then, last-known location and activity history can still help you:
- Confirm the last time the device was active
- Narrow the review to a city or region
- Support internal audit trails and insurance documentation
- Show that security response steps were taken quickly
This is why a stolen laptop workflow is usually about evidence and response, not about pretending you have live surveillance.
How to reduce the risk next time
The best stolen laptop tracker is the one you never need. A basic prevention stack usually includes:
- Asset inventory and device ownership records
- Strong authentication and session control
- A clear incident response playbook
- Privacy-first location history for audits and recovery support
FAQ
How do I track a stolen laptop without GPS?
Use last-known device location at city level together with timestamps, account activity, and audit logs to build an incident timeline. If the laptop reconnects, the last-known record can update again.
Can I see laptop location history?
Yes. With MonitUp, you can review a per-device location history timeline and export records for incident reports or audits.
Is MonitUp real-time tracking?
No. It records the last known active location, not live GPS tracking.
Can VPNs affect stolen laptop tracking?
Yes. VPN exit nodes can show their own city instead of the laptop’s actual city.
Is employee and location tracking legal?
It depends on your jurisdiction and workplace policy. Use clear notice and consent where required, and follow applicable laws. MonitUp is designed for privacy-first, auditable usage rather than covert surveillance.
Where can I learn about MonitUp’s Location Tracker?
Start here: Location Tracking and the broader guide: How to Track Laptop Location on Windows.
Best next step after reading this guide
If your team needs a practical, privacy-first way to review last-known laptop location and location history, MonitUp gives you a cleaner incident-response workflow than relying on guesswork alone.
View location tracking feature | See pricing | Read the broader laptop location guide